MITM Proxy to see my phone’s traffic
Following the instructions from hugotunius.se1, I tried this:
$ brew install mitmproxyand then I run it like this:
$ mitmproxyThis starts a “man in the middle” program, a proxy server that processes every network request and then sends it along to whereever it was ultimately intended.
Then I looked up my Mac’s IP address and set it as a proxy in the iOS/Settings/Wi-Fi under my current wifi network. Just select the i icon and scroll down to Configure Proxy.
Set the Server to your Mac’s IP address, and Port to 8080.
To watch https traffic, you’ll need to install the mitmproxy certificate, which you download at http://mitm.it
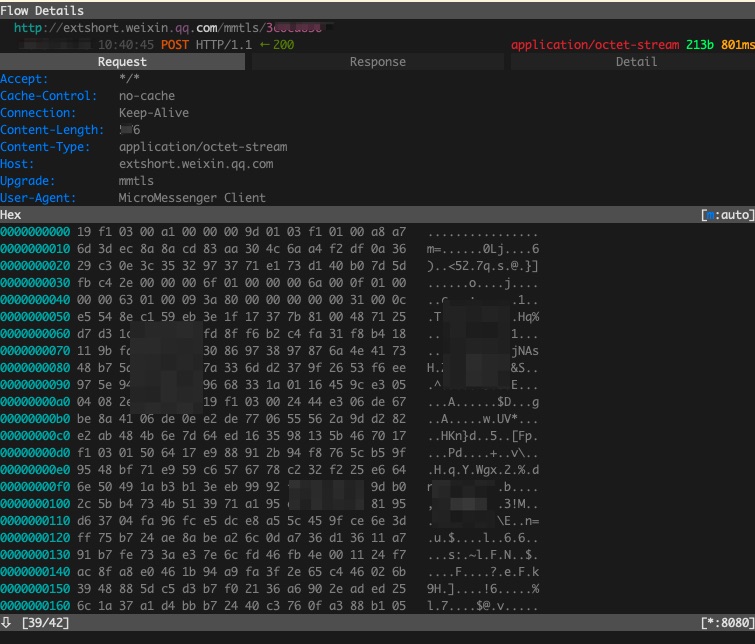
Look at all this information being sent to qq.com (a Chinese server probably connected to my WeChat app):
I’m sure there’s nothing here to worry about. After all, here’s what it says in the app terms of service:
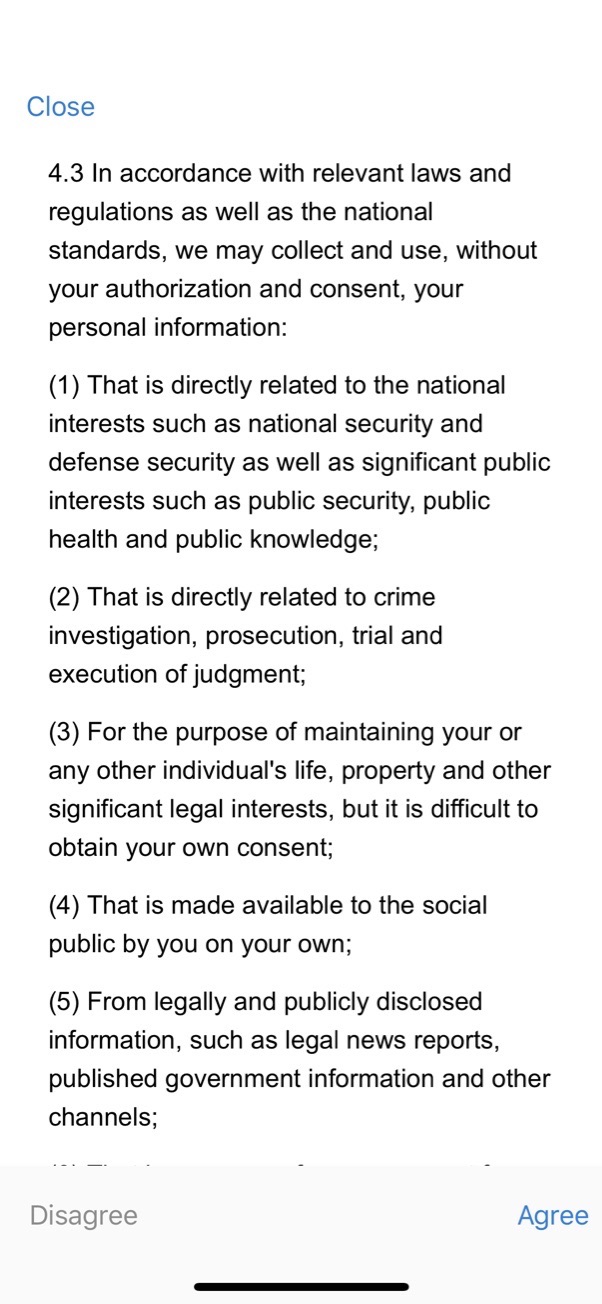
And, uh, in case you’re not paying attention, “national security” in this case doesn’t mean the U.S. Hopefully China is a peaceful country that only has my best interests in mind, cuz somebody over there is collecting a lot of encrypted information off my phone…
and here’s what I smell coming apparently from the app running on that $25 Wyze home security camera I bought thinking it was a good deal.
php@7.2 Flow Details
https://wyze-membership-service.wyzecam.com/platform/v2/membership/check_service_available_by_device
2019-12-19 10:31:39 POST HTTP/2.0 ← 200 application/json 266b 56ms
Request Response Detail
:authority: wyze-membership-service.wyzecam.com
content-type: application/json
appinfo: wyze_ios_2.6.62
accept: */*
accept-encoding: gzip, deflate, br
accept-language: en-US;q=1, zh-Hans-US;q=0.9, ja-US;q=0.8
apikey: ABC1234
content-length: 128
user-agent: Wyze/2.6.62 (iPhone; iOS 13.3; Scale/3.00)
phoneid: <long series deleted>
access_token: <long series>=[m:auto]
[
{
"device_id": "ABC123",
"device_model": "WYZEC1-XYZ",
"feature": "F2,F1",
"firmware_ver": "4.9.5.36",
"sid": "sid_edge_ai_cam_v2"
}
]Footnotes
via Hacker News↩︎